CVE-2025-54236 (aka “SessionReaper”) — What it is, why it matters, and how to fix it
TL;DR
What: A critical bug in Adobe Commerce / Magento Open Source that lets an attacker take over customer accounts via the Commerce API (no login or clicks needed).
Severity: CVSS 9.1 — High impact to confidentiality and integrity; no user interaction required.
Fix: Apply Adobe’s hotfix immediately (and/or update to the latest secure release); Adobe has also pushed WAF rules for cloud customers.
Nickname: Many researchers refer to it as “SessionReaper.”

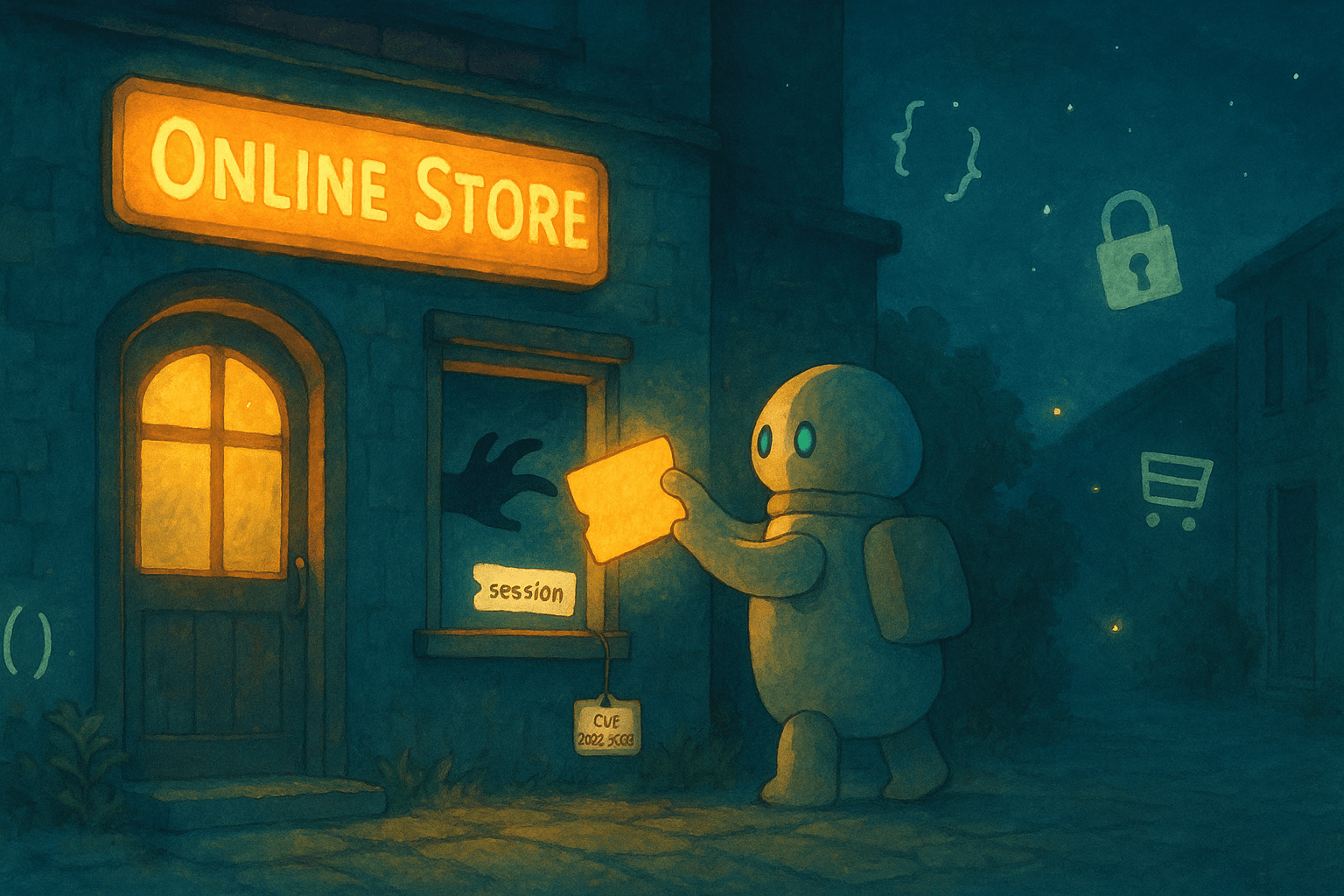
A simple story: “The checkout that trusted too much”
Imagine you run an online store. Your site uses an API to handle customer actions (login, cart, checkout). Normally, the API checks inputs strictly: Is this value a number? Is this field allowed?
Now imagine a sneaky attacker sends a specially shaped API request that slips past those checks. Your site accepts something it shouldn’t, and the attacker ends up walking into a real customer’s account—seeing their orders, addresses, maybe even placing orders as them. That’s CVE-2025-54236 in spirit: poor input validation in the API layer can be twisted into session/account takeover.
What exactly is CVE-2025-54236?
Type: Improper Input Validation (CWE-20) in Adobe Commerce / Magento’s web API path.
Impact: Security feature bypass → session/account takeover (attacker can hijack a customer account without their interaction).
Scope / versions: Adobe lists wide impact across 2.4.x lines (Commerce & Magento Open Source); a hotfix is available and recommended now. Some advisories also mention certain B2B versions and the Custom Attributes Serializable module depending on your setup. Always check Adobe’s current bulletin for your exact version.
Risk level: CVSS 9.1 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:N). In plain English: exploitable over the network, easy to do, no login, no user click, and high data and integrity impact.
Extra context from researchers: Some researchers say that under certain conditions the flaw can be extended further (e.g., towards RCE in complex environments). Treat it as urgent
Why it’s dangerous (in non-technical terms)
No customer action needed: Victims don’t have to click anything.
Steals trust: Attackers can place orders, view addresses, or change details as if they were the real customer.
Hard to notice: Looks like a normal user session in your logs—but it’s not.
Technical deep dive
Root cause (high level)
The web API layer (e.g., REST/GraphQL/SOAP) insufficiently validates nested input structures. With carefully crafted payloads, an attacker can bypass intended checks in request processing and pivot to session takeover. (Researchers point to the ServiceInputProcessor area as key.)
Why authentication isn’t required
NVD’s vector shows PR:N / UI:N — no prior login and no clicks. That means the first request an attacker sends can already trigger the vulnerable code path if the store is unpatched.
What you’d see in the logs (what to hunt for)
- Unusual API traffic to Commerce endpoints (REST/GraphQL) with nested / un
expected JSON shapes.
Account anomalies: multiple sessions for the same customer from new IPs/ASNs close together.
Spike in 4xx/5xx near API auth or customer endpoints, followed by normal 200s for account actions.
(These are general hunting ideas; confirm against your environment and WAF/IDS.)
Vendor notes also mention WAF rules pushed for Commerce Cloud to block known exploit patterns. Check WAF logs for blocks linked to this CVE.

How to fix (priority order)
Apply Adobe’s hotfix immediately.
Adobe published an out-of-band hotfix and recommends updating to the newest secure version as soon as possible. Follow Adobe’s bulletin for steps and compatibility (2.4.4–2.4.7 hotfix package; see latest notes for newer trains).Enable/verify WAF rules.
If you’re on Adobe Commerce Cloud, Adobe has deployed WAF mitigations. Make sure they’re active and monitor for blocks related to this CVE.Audit extensions & custom code.
Even when core is patched, old extensions that touch request processing can re-introduce weaknesses. Review any modules that extend API request handling or customer/session flows. (Vendors warn stores can stay unstable if extensions are outdated.)Rotate sensitive tokens & review sessions.
After patching, invalidate active customer sessions and rotate API keys/tokens as a precaution.Monitor & test.
Add temporary rate limits and anomaly detection on customer/account endpoints.
Create a negative test suite with malformed/nested payloads to ensure the hotfix blocks them.
Sources & further reading
NVD: CVE-2025-54236 (improper input validation; session takeover; CVSS 9.1; UI:N, PR:N).
Adobe Security Bulletin / Hotfix (APSB link; installation guidance, supported ranges, acknowledgements).
Adobe Experience League KCS (account takeover via Commerce REST API).
The Hacker News (overview, affected versions, WAF note, “SessionReaper” name).
Sansec research (technical context; potential for broader impact under certain conditions).
Tenable / CVE Details (concise vendor-agnostic summaries).