CVE-2024-4956 — Nexus Repository 3 Path Traversal (no login needed)
TL;DR
What: An unauthenticated path traversal in Sonatype Nexus Repository 3 lets anyone craft a URL that makes Nexus return any file on the server—even outside the app folder. No login required. Fixed in 3.68.1.
Affected: All Nexus Repository 3.x up to and including 3.68.0 (OSS & Pro). Update to 3.68.1+.
Risk: Exposure of sensitive files (credentials, configs) → possible pipeline compromise; public PoCs exist.
Fix now: Upgrade to 3.68.1+; if you truly can’t yet, apply Sonatype’s temporary mitigations (Jetty change or WAF rule).
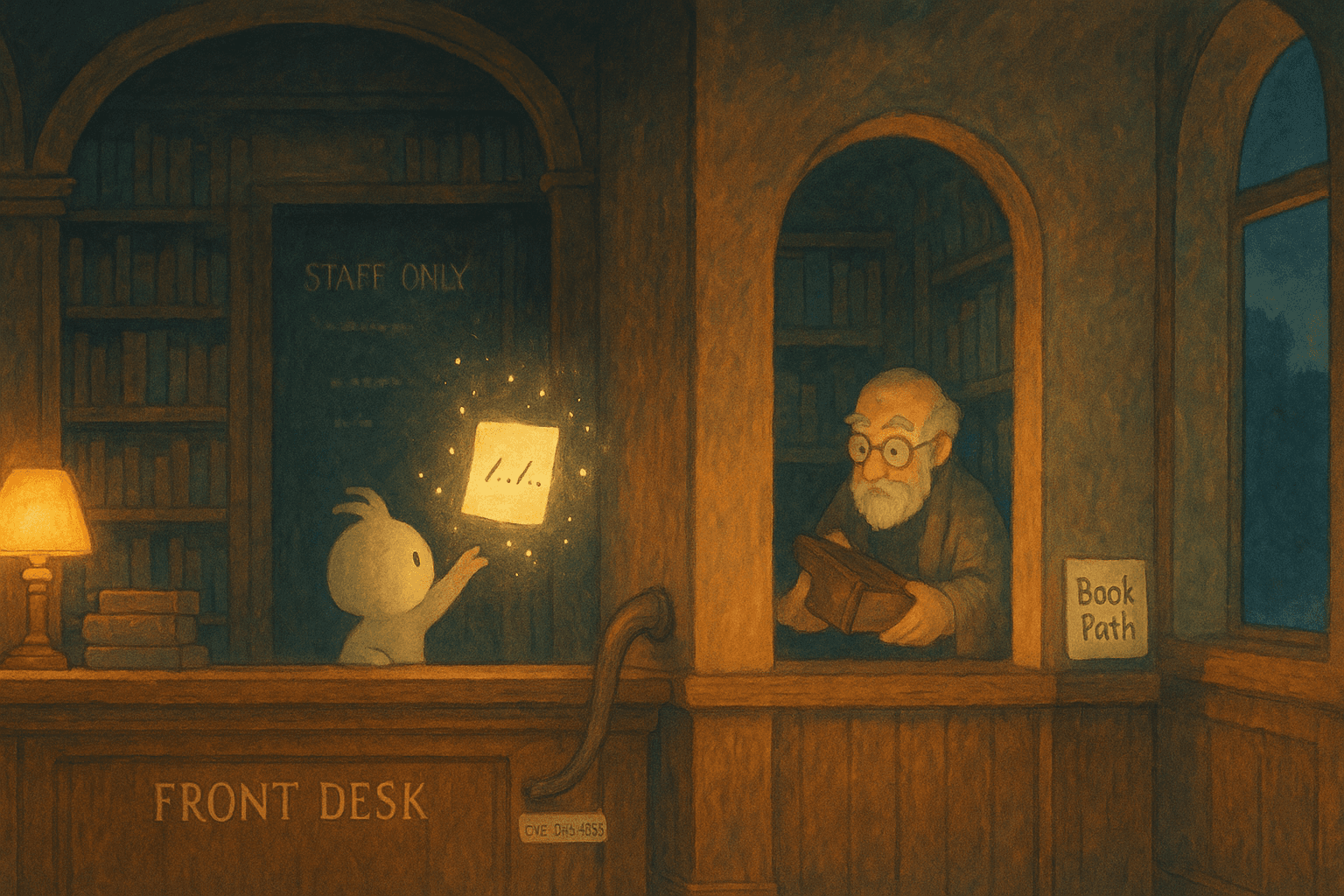
A simple story: “The library window that gave any book”
Think of your Nexus server as a big library. The front desk should hand out only the books that are in the public shelf.
But there’s a side window with a sign: “Give me a note with the book path, I’ll fetch it.”
A stranger slips in a note with a tricky path that walks past the public shelf, down the hallway, and into the staff-only archive. The librarian at the window doesn’t notice the trick; they simply follow the path and hand back whatever book was requested.
That’s CVE-2024-4956 in spirit: the server doesn’t block path segments that escape the public area, so a crafted URL can return arbitrary files without authentication.
What exactly is CVE-2024-4956?
Bug class: Path Traversal (CWE-22). The HTTP handler accepts paths that include traversal sequences, letting a request reach files outside Nexus’s intended scope.
Impact: Arbitrary file read by unauthenticated users (confidentiality impact High). Sonatype/NVD confirm fix in 3.68.1.
Scope: All 3.x up to 3.68.0 (OSS/Pro). Sonatype’s advisory urges immediate upgrade and notes public PoCs began circulating shortly after disclosure.
Why it matters
Secrets exposure: Files like service configs, tokens, keys, or build credentials might be exposed. That can cascade into source theft or CI/CD takeover.
Low bar to entry: No account. A single URL can be enough.
Exploitation in the wild: Public PoCs and scanning appeared days after the advisory. Treat as urgent.
Technical quick look
Root cause: A web route exposed a filesystem-backed resource without properly preventing
../-style traversal (or equivalent encodings), letting requests reach files beyond the app’s public directory.Fixed in: 3.68.1, which removes the unsafe behavior. Release notes call out a critical vulnerability fixed in this version.
Temporary mitigations:
Jetty config change: remove the
resourceBasemapping to thepublicdir inetc/jetty/jetty.xml(side effect: some favicon/asset files won’t load).AWS WAF: enable GenericLFI_URIPATH rule if fronted by AWS WAF; Sonatype verified it blocks known exploit patterns.
How it’s typically exploited
Attacker identifies a public Nexus endpoint.
They send a crafted URL with traversal sequences to request a specific file path.
The server returns the file as a download—even if it lives outside Nexus’s web root. (In vulnerable versions only.)
Note: Exploit DB and various blogs host PoCs, confirming practical exploitation against vulnerable builds. Do not test against systems you don’t own.
Detection: quick wins for defenders
Access logs: Hunt for
../patterns (and encoded variants), unusual requests for/etc/…,C:\Windows\…, or other sensitive paths from the Nexus host OS.Spike watch: Sudden 404/200 patterns or large downloads from unknown IPs targeting non-repository paths.
Robots check for mitigation: If you followed Sonatype’s Jetty mitigation, requesting
/robots.txtshould now return 404 (becausepublic/is no longer served).
How to fix (priority order)
Upgrade to 3.68.1 or newer (recommended)
This permanently closes the vulnerability for all Nexus Repository 3 instances.If you absolutely cannot upgrade yet (temporary)
Jetty config: Remove the
resourceBaseline inetc/jetty/jetty.xml, restart, and verify/robots.txtis 404. Expect minor UI icon issues; they’re harmless.WAF filter: Apply AWS WAF GenericLFI_URIPATH rule if using AWS edge; Sonatype validated this mitigates known exploit paths.
Hardening checklist
Restrict external exposure of Nexus (VPN, IP allowlists).
Put Nexus behind a reverse proxy with LFI/Traversal signatures blocked.
Rotate credentials that might reside on the host if you suspect exposure (Sonatype recommends this out of caution).
Sources & further reading
Sonatype advisory: affected versions, fix, PoC notice, recommendations.
NVD: brief description, CWE-22, fixed in 3.68.1.
Sonatype mitigations: Jetty edit + AWS WAF rule, with verification steps.
Release notes: 3.68.1 “critical vulnerability fix.”
Analyst overviews / PoC discussions: Wiz, SOCRadar, Exploit-DB.
Disclaimer
This article is for educational and defensive purposes only. Test only on systems you own or where you have explicit written permission. Unauthorized access is illegal. Always follow your organization’s change-management process and patch promptly.